Posts in Category: Cyber Attack
What’s Hot in the Home Beauty Device Market
Whether it’s a gizmo designed to help you get rid of acne scars or one that makes your makeup look like you’re wearing actual foundation, the world of home beauty devices is booming. Taking cues from science and medicine, many of these innovations promise results that rival in-salon treatments. As a result, the industry is growing rapidly—in 2022, the home beauty device market is predicted to quadruple in size from about $9.5 billion to almost $92 billion, according to market research firm P&S Intelligence.
Millennials and Gen X are driving growth in the category, but Gen Z is also starting to jump on board with targeted skincare and other devices that help them boost their beauty routines. Some of the most popular gadgets fall into a few categories: those that rely on light therapy, such as ledmasks or the new MMSphere 2Go from MZ Skin; microcurrent and other technologies that use low levels of electricity to lift and tone muscles, which include products like NuFace’s Trinity+ or the viral four-in one wand that made its way to TikTok fame; galvanic current, which sends a different type of electric charge into the skin to boost blood circulation and promote cell renewal; vibration therapy, which uses sound waves to stimulate the skin and tone muscles; radiofrequency treatment, which sculpts and tightens, including on the neck and jawline.
Most of these devices are relatively easy to use. The trick is using them consistently to see results (and avoiding overuse, which can cause irritation and even permanent damage). Fortunately, most of the hottest beauty tech devices have been through rigorous pre-approval safety testing before hitting shelves. But as the category evolves, it can be tricky to figure out what’s right for you.
The most popular beauty devices are those that help elevate your favourite skincare and makeup, ensuring they work as hard as possible. Cleansers, for example, come in a range of options, from Foreo’s Luna 3 that pairs with an app to guide you through a 60-second cleanse to the new HiSkin, which dispenses skincare into the skin and hair via patented diffusion technology.
Others address specific concerns, such as reducing the appearance of fine lines or unclogging pores. This year, a new generation of gadgets emerged that offer solutions that are similar to a hydrafacial—such as the new Migraine & Ingrown Hair Remover from Neuma, which combines deep-cleansing salicylic acid with blue LED light to clear away blackheads and whiteheads https://beautyfoomall.com/products/cellreturn-platinum-led-mask.
While some of these gadgets are quick and simple to use, others can be complicated and may require a bit more training. Still, many are safe for at-home use and can help you achieve noticeable results in a few short weeks or months, as long as you follow the instructions. As with any new product, however, it’s best to ask a dermatologist or esthetician for advice before buying one. (And, of course, always be sure to wear protective eyewear while using these tools.)
…Why Install CCTV at Home?
If you’re looking for ways to protect your home, you might want to consider installing a CCTV security system Singapore. These devices have several advantages over traditional security cameras, including their ability to provide real-time monitoring and recorded evidence in the event of a crime or emergency.
Preventing burglaries: The presence of a security camera will act as a deterrent to criminals and discourage them from trying to break into your house. In fact, a University of North Carolina at Charlotte study found that homes without security cameras had an 85% chance of being broken into while those with security cameras had only a 30% chance.
Keep your family safe: CCTV cameras can help you prevent crimes like sexual assault, stalking and bullying. They also have the ability to record audio and video which will work as strong evidence in court if someone does try to attack your family.

Keeping your kids safe: A CCTV camera system can make sure your kids stay safe at home while you’re away. It can even help you monitor them remotely so that if something happens, you’ll know about it immediately.
Avoiding fires: There are many new models of security cameras that come with fire detection features, ensuring your home stays safe. They can detect heat coming from a fire and alert you of the source. This can save you money and reduce your risk of getting burnt.
Save money on insurance: Most insurance companies will reduce your premium if you install CCTV in your home. You can also use the footage to prove your insurance claim in case of a burglary or robbery.
Protect your property from thievery: If you have a lot of valuables, CCTV is a great way to protect them. It will help you get the most out of your insurance policy and avoid paying for items that have been stolen.

Reducing your insurance cost: If you live in a high-crime area, you may be able to receive discounts on your home insurance through CCTV. It’s worth calling your insurer to find out if you qualify for these discounts and how much you can expect to pay.
Adding a touch of elegance to your home: The installation of a security camera will add a unique touch to your house and improve the appearance. It can help you sell your house or even rent it out, as it will be more appealing to potential buyers.
Deterring criminals: If a criminal has seen your security camera and decided that it’s not worth the risk of breaking into your home, they’ll likely move on to another home. In fact, a recent report showed that 60% of burglars enter houses through the front door and just 30% through windows.
For this reason, it’s crucial to point your security cameras towards these entrances and exits so that they’re constantly monitoring them, even when you’re not home. Having a security camera installed is a great way to deter criminals from your home, so make sure you have one or more in place today!
…Common benefits of touch-screen technology
Common benefits of touch-screen technology
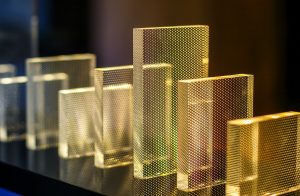
One of the biggest advantages of touch screen technology is its perceptive interface in between both the user and the device. People today are utilizing this technology not just for businesses but residents are also opting for touch-screen at a faster pace Smart Glass technology. This touch screen is a new standard today if it’s a phone or tablet. Touch screens are not just affecting our working process but our home life is also affecting a lot and not in a negative way. Touch screen in residential sector is gaining immense popularity. Starting from refrigerators to washing machines, everything comes with a touch interface. Slowly and steadily, touch screens are becoming a vital part of our lives and it’s assured that they will be a strong part of our future too. So, let’s have a look at the advantages that touch-screen technology has to present.

Speed is the foremost benefit. Touch screens allow devices to function much better and efficiently. Touch-screen takes less time as compared to computers and laptops. Touch-screens have really speeded up the working processes Chiefway. Saving few seconds on one task actually adds much to your precious time.
Easy to use is another benefit. It’s proven across the world that touch screen technology is convenient to use. And this technology even eliminates errors. It allows multiple- tasking as using a touch-screen; you need not type the instructions which it needs to follow to give you adequate results. There are numerous touch-screen devices that you can use with stylus pens or other pointing devices.
Some people are so used to touch-screens; they carry them their screens wherever they go. It is quite a nice option with touch-screens as with computers and laptops; it is difficult to pick them up everywhere. With touch screens, you just have to tap the application that you want to open; not any kind of struggle is there in this. Touch screens have made people digital experts as things are quite easy to understand. Touch screens have made things run smoothly and efficiently.
This technology is the all-in-all solution for almost all tasks. These screens are available in all shapes and sizes. Touch screens today are not just confined to phones and tablets. With this technology, screen size is not at all a restraint now. The best part is that all you require is a charging wire to operate this device to its fullest.

Durability: – Different touch screen technologies provide different protective features. The screens in this touch-screen are particularly made of glass or some polyester surface. This type of material is easy to clean and maintain and thus is perfect to use in public places. They are highly durable and thus are perfect for office use, residential use, and at numerous other places also.
This is all about touch-screens and their common benefits which both residentials and officials can enjoy. So, get in touch with this touch-screen technology today and see things getting innovated around you.
…How a Promotion in Casino Can Increase Your Chances of Winning
How a Promotion in Casino Can Increase
Your Chances of Winningslot games
The types of promotions available at a casino vary. Some offer no-deposit bonuses while others
may give new players free spins or points multipliers slot games Malaysia. It all depends on which type you prefer. In
any case, a good promotion at a casino will boost your chances of winning. To find out how to
maximize your chances of winning, read on. You can also use the information on the website to
choose the right casino. If you like playing online games, a promotion at a casino can be a great
way to increase your chances of winning.

Free sign up bonuses
Many online casinos offer free sign up bonuses to entice new players. These bonuses are
typically worth as much as $100. In addition to being free Sportsbook Malaysia , they can also be used to play for real
money, allowing you to cash out any winnings without any risk. The terms and conditions of
these promotions vary greatly, but you can generally expect the same general rules and
regulations as for any other online casino. Here are some important tips for taking advantage of
these offers.
The 10x the bonus has more strict wagering requirements. For every $1 in free signup bonus,
you must wager at least $10. Different online casino games contribute differently towards
wagering requirements. For example, online slots, lottery, keno, virtual sports, and baccarat
count 100%, while blackjack and other table games only contribute 20%. Roulette and video
poker, which typically require a lower wagering requirement, count as a single digit percentage.
No-deposit bonuses
Online casinos offer casino no-deposit bonuses to entice new customers and increase sales. No
deposit bonuses are usually in the form of free spins or money. New online casinos may use
these offers as a way to attract new customers and create a loyal following. These free spins or
money are a great way to test the waters of a casino without spending any money. Other
casinos may offer no-deposit bonuses to compete with rivals or remind existing customers that
they exist.
While the terms of casino no-deposit bonuses vary, the majority require that the players wager
the bonus within a certain time frame. Most no-deposit bonuses can range from ten to twenty
percent of a player’s deposit. It’s important to remember that no-deposit bonuses are not meant
to be monetary winnings, so they’re not considered real money. However, many people don’t
realize that these bonuses can actually give them money!

Free spins
A free spins promotion is a great way to attract new players to an online casino. Free spins are
used on a wide variety of slot games. Since players like to try different kinds of games, casinos
need to offer free spins on the best titles. If you are looking for a free spins promotion, you can
find hundreds of them at online casinos. Here are the basics of these promotions. You can use
them to win big prizes.
Bonus spins are given to you as a welcome gift after making your first deposit. These free spins
can be used on different slots and can be redeemed with a variety of bonus offers. The terms
and conditions of these bonuses are usually quite easy to understand. Bonus spins are given
out after a specified deposit amount is made, while no deposit free spins are given out upon
registration. The best way to choose a casino with a free spins promotion is to read the rules and
regulations carefully.
Points multipliers
When it comes to casino promotions, point multipliers are a great way to help you get ahead.
Comp points are basically scorecards for tiers. Once you have enough comp points, you can
redeem them for free play or comps. Some casinos focus on tier credit multipliers, while others
offer both types of promotions. There are some important considerations to make when
considering a point multiplier. Listed below are some examples of the ways a casino can use
point multipliers to help its players get ahead.
Some casinos limit which games count towards a particular point multiplier. Some casinos
exclude table games, video poker, and wide-area progressives. You should find out which
games are excluded from a given point multiplier before participating in the promotion.
Regardless of whether you are participating in a casino loyalty program or a different type of
promotional program, it’s a good idea to understand what the specific rules are for a particular
casino.
New York Online Sports Betting
New York Online Sports Betting
When you bet online, you are in control of your betting experience 新加坡网上赌场. Whether you are betting on
football or basketball, you will be able to see the odds, place your bets, and monitor your
winnings. You also don’t have to deal with the hassle of dealing with a land-based bookmaker.
There are several options available. You can sign up for free at several different online
sportsbooks. However, you should always be careful to read the terms and conditions.

The first step in online sports betting is to sign up with a licensed bookmaker. This will save you
a lot of time. Most sportsbooks will accept deposits through credit card 新加坡网上投注, while others will only
accept cash deposits. You can also make deposits using your debit card. Most sites will accept
payments via wire transfer or PayPal. Depending on the type of gambling site you choose, the
amount you deposit will be different. You should also consider the security and customer
support before deciding to sign up.
While online sports betting can be a lucrative business, it isn’t without risk. While some people
may be lured by the huge profits of online sports betting, some players might not know how to
protect their personal information. Moreover, there’s little privacy protection with this type of
gambling. Many sites are not willing to provide you with all the necessary information regarding
their terms and policies. This makes it impossible to know whether you’re safe in playing or not.

Online sports betting isn’t regulated. The state lottery doesn’t have the authority to regulate the
industry. In addition, it is a source of revenue for the lottery, which means that the state will have
no legal liability for any disputes. It’s not illegal to play online, but you must have an account with
a reputable betting site to participate. While many states have laws governing sports betting,
New York is the only state to have a regulated version.
There are advantages and disadvantages of online sports betting. One of them is that it’s
possible to earn a lot of money. In fact, New York sportsbooks brought in more than $3.57
million in gross revenue in January alone. Despite this initial bump in the state lottery, however,
the governor of New York has publicly expressed his support for online sports betting and the
single-source model run by the state lottery. While the single-source model has been heavily
criticized in Washington, it does not have a clear benefit for consumers.
New York’s sports betting market has experienced a tremendous start in 2021. A total of $10.7
million in sports betting revenue has been recorded in the state through January of this year. As
such, the state’s Governor has expressed his support for the industry and the online versions.
Moreover, he has endorsed the single-source model run by the state lottery, which has been
heavily criticized in Washington D.C., as it tends to result in higher prices for consumers.
The Gold Betting Casino Review
The Gold Betting Casino Review
Betting casino games is a popular pastime that offers a high degree of luxury and elegance. The
site is devoted to gold bars and golden winning opportunities online casino games. You can play games instantly in
the casino thanks to flash technology, which allows for a high quality gaming experience. The
site welcomes US players and uses Wager 21 software. The website also features live chat with
a customer care representative. There are a variety of betting options available, including sports
betting, horse racing, and casino baccarat.

The Gold Betting Casino has a luxurious look and uses the Wager 21 software. This software
offers a good selection of games, including slots, video poker, and table games. It has a decent
welcome bonus and 25% extra when you top up. There are only a few banking methods
available, including credit/debit card and Neteller, which is a convenient option for many players.
Moreover, there is poor customer support. The website only provides email contact details,
which makes it feel less reputable than other sites.
The Gold Betting Casino is a great choice for those who love to play casino games and have an
appetite for a luxurious look. It uses Wager 21 software, which gives a decent selection of
games. You can find a welcome bonus of up to 200% and get another 25% when you top up
your account. One downside of the site is that there are only two banking options available –
credit/debit cards and Neteller. This makes the site feel less trustworthy than some of the other
sites.
The Gold Betting Casino has a luxury look and uses Wager 21 software. The casino offers a
good range of games, a nice welcome bonus, and a 25% top up bonus. However, there are
some drawbacks. While the site offers a decent welcome bonus and a good range of games, it
does not have a good customer support system. They only provide email contact details. This
makes it feel less secure than other sites.

The Gold Betting Casino is a luxurious site with a very impressive interface. The site uses Wager
21 software and features a good selection of games. The site offers a 200% deposit bonus for
new customers, which is great for those who are looking to play online. Aside from a generous
welcome bonus, Gold Betting Casino also offers a good bonus for reloading. Its payment
methods are limited, but you can use credit/debit cards and Neteller for making deposits. The
customer support is also not the best. The contact details are only available through email,
making the site less reliable than most.
The Gold Betting Casino has a very luxurious appearance, which is always a plus. The software
used is primarily designed for gambling. It also offers a good welcome bonus, where you can win
a lot of money. There is also a wide range of games to choose from, which means that it’s
possible to find something that suits your style and budget. The casino also offers customer
service through email, so it’s important to contact the site’s customer support department if you
need help.
Bet Live Casino Review
Bet Live Casino Review
The Bet Live Casino offers a variety of casino games that allow players to win real cash. They
also feature progressive jackpots that can reach hundreds of thousands of dollars live casino India. The bonus
zones at Bet Live Casino can be a good place to redeem bonuses or free spins on all games.
There are a few risks when playing in a live game, so it is important to practice until you feel
comfortable and confident enough to bet with real money.

The betting options available in the Bet Live Casino are vast and it is vital to know what you’re
betting on. You can use the bonus money to bet on games at live tables https://www.mmc9696.net/in/en-us/product/livecasino, but you cannot
withdraw your bonus until you have played a specified number of live games. You can use your
free bonus money to play at the live tables, but you must make sure you play with real money in
order to withdraw it. The terms and conditions of the free bonuses vary so it is important to read
them carefully before depositing real money.
Another risk is that BET Live Casino is a smaller online casino than its online competitors.
However, revenue is an important factor. A larger online casino will have no problem covering
big winnings, while a smaller one may struggle to do so. Furthermore, BET Live Casino BA has
a smaller customer base than its online rivals, which may cause a problem if a player wins large
amounts of money. Aside from this, the website’s main purpose is to draw attention to unbiased
reviews by gambling experts.

When it comes to live casino betting, you need to choose wisely and know your odds. If you’re
unsure about the odds, you should read the Bet Live Casino terms and conditions. For example,
if you’re using a bonus to play at a live table, you can’t withdraw your winnings until you have
played a certain number of real-money games. You should always remember that there are
limits for the bonuses you can receive and use.
Aside from being smaller than its online competitors, BET Live Casino offers a lot of different
betting options. Knowing the odds of each game is a great way to choose a game that is best
suited to your budget. Besides, it will give you the opportunity to meet new people and enjoy live
gaming. And while it may not be as popular as some of its online rivals, it offers a high-quality
experience.
If you are a live game enthusiast, you’ll love the Bet Live Casino. Its extensive library of over
thirty of the best solutions from Evolution Gaming, Ezugi, Vivo Gaming, and BetGames will
surely make you happy. In addition to its impressive collection, the Bet Live Casino’s live casino
software also makes it easy to find a wide range of different games. If you’re not sure which ones
to play, you can always visit the website of one of the many live casinos and see if there are any
helpful tips and tricks.
5 Reasons Why Women Should Take Supplement Pills
5 Reasons Why Women Should Take Supplement Pills
Why women should take a supplement is a question that I get asked quite often home skin tightening device. Some people will tell you they would never suggest a woman
even try a weight loss supplement, but others will tell you the very same thing. The reason the latter two people are both correct is simple – it’s
just a question of biology. Let’s quickly go over what happens when we take in more calories than we use up.

First off, women have a greater amount of subcutaneous fat than men do, which explains why we store more fat under our skin as well as our
belly and hips. Women also have a higher rate of insulin sensitivity beautyfoomall.com, which means that the glucose in our system doesn’t immediately get to the
muscles in order to provide us with energy. This makes us want to eat more, leading to weight gain. Taking a supplement that increases insulin
sensitivity will help increase your ability to handle insulin, which means less fat stored and less weight lost.
Another reason why women should think about using a supplement is because the average man requires about one gram of protein for every
pound of body weight, while women require about one gram for every two pounds. The reason for this difference is that women store fat much
differently than men do. Men are basically protein machines, working primarily on the muscles, while women are primarily fat machines. This
means that unless you eat a large amount of protein with each meal, your body will begin to feel the effects of muscle growth and will need
extra protein in order to keep going.

It might also be smart to take a supplement if you are an athlete. Because the supplement industry is legally bound to list all of their products
as prescription drugs, many supplement companies to include nutritional information about how and when you should take their products. For
example, if you are training for a particular event, you may want to make sure you are taking the right amounts of protein, calories, vitamins,
and minerals.
The last reason why women should take supplement pills is because of the harmful side effects that can occur from using them. Common side
effects can include the following: depression, bloating, dizziness, diarrhea, nausea, and even memory loss. All of these effects can be quite
serious, which is why women should first consult with their doctor before they decide to add a supplement to their diet. While there are some
rare, life-threatening side effects associated with many supplements, this is not the most important thing a woman needs to know when it
comes to choosing a supplement for herself.
In conclusion, it is simply not true that all women can use supplements to lose weight. Even if you take them in conjunction with eating a
balanced diet, a healthy exercise program, and drinking lots of water, you will still have to be careful. While they may be good for your health,
they should not be relied on as the sole source of your weight loss efforts. Women who are interested in slimming down and staying healthy
should consider all of their options, including trying a healthy supplement.
Scientists create light waves that can pass through even solid objects
 The behavior of light can tell scientists several things. Like for example, making sure the sugar is not transparent. That’s because the light that penetrates it is scattered, altered and deflected in a very complicated way.
The behavior of light can tell scientists several things. Like for example, making sure the sugar is not transparent. That’s because the light that penetrates it is scattered, altered and deflected in a very complicated way.
However, a research team from TU Wien in Vienna and the University of Utrecht in the Netherlands managed to show that there is a class of very special light waves that this normal behavior does not apply to. In this class, bespoke light beams can be created and are practically unaltered by the medium they pass through, just attenuated. The beam of light penetrates into the middle and a light pattern arrives on the other side with the same shape, as if the middle were not there.
These types of scatter-invariant light modes can be used to specifically examine the interior of objects.
Waveforms
Waves on the surface of water can have an infinite number of different shapes. Just like light waves, they can also be made in many different ways. “Each of these light wave patterns is altered and deflected in a very specific way when you send it through a cluttered medium,” explained Professor Stefan Rotter, from the Institute of Theoretical Physics at TU Wien.
Stefan and his team are developing mathematical methods to be able to describe the effects of light scattering . “As a light scattering medium, we use a layer of zinc oxide, an opaque white powder of completely randomly arranged nanoparticles,” explained Allard Mosk, head of the experimental research group.
“As we have been able to show, there is a very special class of light waves, called scattering invariant light modes, which produce exactly the same wave pattern in the detector, regardless of whether the light wave was sent only through the air or if it had to penetrate the complicated zinc oxide layer,” said Rotter.
“In the experiment, we see that zinc oxide doesn’t really change the shape of these light waves at all. They are a little weaker in general”, highlighted Mosk.
Experiment
And as rare and special as these invariant light modes are, and having a theoretically unlimited number of possible light waves, you can still find many of them. And by combining several of these invariant light modes into a right arrangement, the result will be a scattering invariant waveform.
 “This way, at least within certain limits, you have a lot of freedom to choose which image you want to send through the object without interference. For the experiment, we chose a constellation as an example: the Big Dipper. And, in fact, it was possible to determine an invariant wave that sends an image of Ursa Major to the detector, regardless of whether the light wave is scattered through the zinc oxide layer or not. For the detector, the light beam looks almost the same in both cases,” said Jeroen Bosch, who worked on the experiment as a doctoral student.
“This way, at least within certain limits, you have a lot of freedom to choose which image you want to send through the object without interference. For the experiment, we chose a constellation as an example: the Big Dipper. And, in fact, it was possible to determine an invariant wave that sends an image of Ursa Major to the detector, regardless of whether the light wave is scattered through the zinc oxide layer or not. For the detector, the light beam looks almost the same in both cases,” said Jeroen Bosch, who worked on the experiment as a doctoral student.
Comments
This method of finding light patterns that penetrate a large, undisturbed object can also be used for imaging procedures.
“In hospitals, X-rays are used to look inside the body. They have a shorter wavelength and therefore can penetrate our skin. But how a wave of light penetrates an object depends not only on the wavelength, but also on the waveform. If you want to focus light into an object at certain points, then our method opens up completely new possibilities. We were able to show that, using our approach, the distribution of light within the zinc oxide layer can also be specifically controlled,” concluded Matthias Kühmayer, who works as a doctoral student in computer simulations of wave propagation.
…Stay on top of the worst cyber attack hackers have ever launched
 Recently, we’re seeing diplomatic tension between the United States and Russia, right? Yeah, those who haven’t noticed, know: both nations aren’t pecking at each other at the moment. The reason is simple but difficult to swallow. After all, we’re not talking about two boys who fight over a toy and come to terms with each other again, when their parents arrive and put some order in the room. We are talking about two world powers .
Recently, we’re seeing diplomatic tension between the United States and Russia, right? Yeah, those who haven’t noticed, know: both nations aren’t pecking at each other at the moment. The reason is simple but difficult to swallow. After all, we’re not talking about two boys who fight over a toy and come to terms with each other again, when their parents arrive and put some order in the room. We are talking about two world powers .
To better understand this disagreement, it is necessary to go back to 2020. That’s right. Last year, hackers, directed by the Russian intelligence service, the SVR, in addition to having access to the system of SolarWinds, an American company that basically develops software, were able to insert malicious code into one of their products. This attack, today, is being considered as one of the worst in history.
Hackers
“We believe that between March and June 2020, eighteen thousand customers may have downloaded this product that has been corrupted,” said Sudhakar Ramakrishna, President and CEO of SolarWinds, in an interview with NPR. “If you take that estimate and start looking at it, the actual number of customers affected will be smaller or larger. We don’t know the exact number, we just have an idea. We are still conducting the investigation.”
The investigation was completed this year. Ramakrishna calculates that the Russians have committed – and successfully – about 100 companies and a dozen government agencies. Companies include Microsoft, Intel and Cisco; and the list of federal agencies so far includes the departments of Treasury, Justice and Energy, and the Pentagon.
Regardless of the damage, on Thursday, April 15, the Biden government announced a list of tough sanctions against Russia – that is, a response to the breach of the SolarWinds system.
Even listing some sanctions, the concern remains, mainly on the part of the Cybersecurity and Infrastructure Security Agency, or CISA – Department of Government Security whose job is to protect federal computer networks from cyber attacks, but that failed.
Attack
The action of the hackers involved in the attack was strategic, well thought out. In order for the plan to work, the ‘victims’ needed to first download an update of contaminated software and then update it. Then the compromised networks needed to be connected to the Internet, which would help hackers communicate with servers.
The software that was affected and functioned as a fundamental part of the operations was Orion. The program in question is commonly used by US information technology departments and that’s why hacking it was a more than ingenious strategy.
“This was, without a doubt, our worst nightmare,” said Tim Brown, SolarWinds vice president of security recently. “It’s kind of a horror movie. In addition to affecting thousands of customers, it caused damage that is still unimaginable.”
Cybersecurity experts compare the current damage to an attack that took place in 2017, when the Russian military gained access to a ransomware known as NotPetya. Like Orion, NotPetya software was also corrupted, but the action to date has paralyzed activities of multinational companies and permanently blocked tens of thousands of computers worldwide.
SolarWinds
The investigation carried out by the authorities that work in the intelligence departments of the United States indicates that SolarWinds is living the same scenario, after all, the hackers had enough time to cause several damages. Hackers are estimated to have enjoyed American computer networks for nine months. It is not yet known whether the activity was restricted to just reading emails or whether the action boils down to destructive behavior.
The hackers who hacked into the SolarWinds system gave a masterful lesson in new hacking techniques: they modified the Orion software code, created a system that used domains to select targets, mimicked the software’s communication protocols, and finally cleaned up the crime scene so investigators could not definitively prove who was behind the attack.
“The strategy was phenomenal,” said Adam Meyers, a forensic expert appointed by SolarWinds to analyze the corrupted software. “The work was elegant and innovative, which makes it even crazier.”
The conclusion of the current investigation, coordinated by the White House, blames Russian intelligence. Russia, for its part, denied any involvement.
…



